William Weber, a LowEndTalk member, was raided by Austrian police in 2012 for operating a Tor exit node that was allegedly used to distribute child pornography. While he was not arrested, many of his computers and devices were confiscated. He was later found guilty of supporting the distribution of child pornography through his Tor exit node, though he claims it was unintentional and he was simply supporting free speech and anonymity. He was given a 5 year probation sentence but left Austria shortly after. Though some articles portray him negatively, it is debatable whether he intentionally supported child pornography distribution or simply operated in the legal grey area of Tor exit nodes.
We oughtta arrest the people who pave roads because human traffickers use them to commit crimes.
I wonder if the ISP got charged as well lol
From the article…
Yes, as they had to give me the minimum sentence. By law they were right as the law only protected registered companies, unlike in Germany for example. The law was changed a few weeks later to include private persons and sole traders as protected lsps, not just companies, but they had to convict me. No choice in the end.
So, ISPs in Austria actually have legal protection from liability here, rightfully so, and also rightfully so, that protection was extended to private persons as well. A rare story of a legal system apparently working well, with regard to the marriage of privacy and technology.
The law was changed a few weeks later to include private persons and sole traders as protected lsps, not just companies, but they had to convict me. No choice in the end.
I am not sure I would consider this “working well”. It is the job of the court to determine if and how to apply law. Laws are never perfect and should be applied per intention, and not word-for-word. If the latter would even be possible, we wouldn’t need judges in the first place, because it would be a “simple” decision tree. But it’s not. And we have judges and the court processes for a reason.
If the law was amended a few weeks later, it shows, IMO, that the intention of the law was different than what was written down. Therefore the judge should have ruled that way by acknowledging that while the law does not exempt private individuals, its intention shows that it clearly should (simply because it doesn’t make much sense otherwise).
In other words: if the system really worked well, the judge would have sentenced (or rather not sentenced) within the intention of the law, and not within the strict writing.
(Worst case is that something like that gets escalated to the highest court who then either also accepts or overrules it.)
Yep given this is Austrian jurisprudence they should be able to apply Radbruch. Could it be overturned on appeal? Sure, but the judge also wouldn’t look stupid on appeal. German courts are using it in instances like conjuring a Romeo+Juliet exception out of thin air (in the “sex on your 14th birthday with your SO who is still 13” kind of sense), directly contradicting written law, saying “yep they overlooked that corner case”. Law didn’t even get updated as application of the formula is so uncontroversial.
In particular, this letter-of-law interpretation ignores equality before the law – that between natural and juridical persons. You need a proper reason to do such a thing. Quoth Radbruch:
Where there is not even an attempt at justice, where equality, which forms the core of justice, is deliberately betrayed in the laying down of positive law, then the statute is not even merely ‘flawed law’—rather, it lacks completely the very nature of law. For law, including positive law, cannot be otherwise defined than as a system and an institution whose very meaning is to serve justice.
Do they not have Jury Nullification over there?
Can’t have jury nullification if you don’t have juries.
The charges usually end up falling onto the last one who can’t stick them onto someone else.
Like, a carrier can blame the ISP, who can blame the VPN, who can check its logs and blame an address owner, who… better keep their own logs capable of identifying someone else if they’re letting random people do random stuff using that address. And a good lawyer, and will and money to fight it.
It sure is weird how a political system based around who has the most money always ends up hurting the people that don’t have money. Nobody could’ve predicted that.
Is there really a realistic way to do it differently? Situations ending up in court are complex and ambiguous. It’s never a simple “if this then that” kind of thing. So in the end it’s about making arguments and convincing each other. Different people have different skills and depending how you match up, arguments are lost or won. There will always ever be a limited amount of extremely skillful people. Even if you would make sure that money isn’t a barrier, time/availability will still be and so still most people will end up with inadequate council.
If a justice system is so hard to use that only a small portion of the trained professionals can do it adequately it needs a massive overhaul. This of course is basically impossible and won’t happen. The US is a particularly bad case because of the sheer outdatedness of its constitution an court procedures.
I think most laws started out simple. Reality isn’t simple, however. And I would bet that any attempt to simplify it will be adjusted over time and will end up being just as complicated again.
I mean, the law could be simple in the sense that it basically says “don’t to stupid shit”. But then it just becomes more subjective which in the end will be even less fair.
All the complexity in the law comes from the attempts to make it as fair and objective as possible.
Don’t have a society that gives all the power to people who have the most imaginary tokens. Don’t assign and apportion legal counsel according to money but instead according to need. Like, obviously I’m criticising capitalism, but your question assumes capitalism is here to stay.
Of course, under capitalism this will never happen, because the legislature is thoroughly captured by capital, and they are quite happy with lawyers being extremely expensive and siloed away in massive corporate legal teams.
Now of course none of what I am suggesting is going to be easy, quick, or absolute, which I mention just to head off the inevitable critcisms along those lines from people who find it easier to imagine the end of the world than the end of capitalism. As Ursula K le Guin said, “We live in capitalism, its power seems inescapable – but then, so did the divine right of kings.”
but your question assumes capitalism is here to stay.
It does not. In my last sentence I specifically said “Even if you would make sure that money isn’t a barrier”, which rules out capitalism. So in a system where everyone has equal access to everything, you still only have a limited amount of skilled people with the right profession. If there are currently 1000 first-degree-murder cases where life sentences are on the line, and you only have 10 extremely good lawyers … 990 people will still end up worse than the 10 that had the luck (!!) to get these 10 good lawyers assigned.
Shouldn’t all social media, ISPs, Apple, Google, etc also be found guilty of the same crime then? What about CDN?
you see, they are companys and they make monzees that they dont pay taxes on, so its fine. But that guy was a terroristic web activist, subverting the order of the free world by providing free tools to a community of which some used it for illegal purposes.
The article explains that this was basically a flaw in the way the law was written
Reading the article, it’s not just distributed CP. Someone also used his Tor Exit to hack into a NATO facility in Poland that dealt in chemical/biological weapons. Like, yeeesh.
This “someone” sounds an awful lot like a nation-state actor.
Yikes 😬
The absolute balls on the man to continue after being raided. It’s unfortunate that the private internet requires people like him to risk their safety so it can continue to operate.
I am from austria and honestly I feel ashamed. What honestly gets my blood boiling is the fact, that there is a high chance the people that connected through his exit node are probably still free.
It is like jailing the postman for delivering a letter containing CP. Anyway I hope the people actually actively distributing and using CP get what they deserve.
You shouldn’t feel too ashamed, in the end Weber got 5 years of probation on the sentence of “support of general distribution”, and shortly after the law was amended to give private persons like Weber the same protection from liability that ISPs enjoy from how people use their network. At least, according to Weber.
Here the crime is privacy, which is the same thing many countries are trying to curtail, including France, which is clamping down hard on encryption.
With time we will see services like protonmail or vpns vilified in order to make them inaccessible to the public.
I’m surprised this doesn’t happen more often. Home routers are trivial to compromise, and compromised home routers can also be used to distribute illegal content.
This is equivalent to a criminal running into a crowd to get away from police, and the police just stopping, arresting, and charging the first person in the crowd that they see for not doing anything to stop them.
I always read this is why you run a relay as an individual not an exit. Some one has to run a exit at some point though.
You don’t need an exit node to browse Tor hidden sites. Acting as a relay middle node is also not a problem.
Exit nodes are kind of a “plausible deniability” thing for Tor users from places where using Tor might be frowned upon, but otherwise you can find anything you may want to use Tor for, on hidden sites themselves.
For as much as I’d like to help the Tor network and the idea of free speech, articles like this are why I’d rather let the CIA and other national sponsors take the brunt of running those exit nodes.
But someone somewhere has to be an exit node. Not you, necessarily, in order to browse, but somebody has to be running them. Right?
Tor hidden sites are hosted on Tor nodes, so you don’t leave the Tor network to browse them.
Anyone with a Tor node can host a hidden site, and there are some more or less famous ones around. Some open web sites keep a hidden one as an alternative in case their domain gets taken down or blocked for whatever reason in whatever country.
Only to connect back to the normal internet. Entry nodes are different (no clue if you can do both on the same server or not.
Btw, what’s the current judicial status of exit nodes around the world? Why was he charged, yet the isp wasn’t? Would the isp be charged if it ran a similar exit node, or is it strictly because it was a private entity?
Rule of thumb: You get the blame.
TL;DR: Ask a lawyer.
You can compare them to VPNs for the severity of restrictions (in 2020):
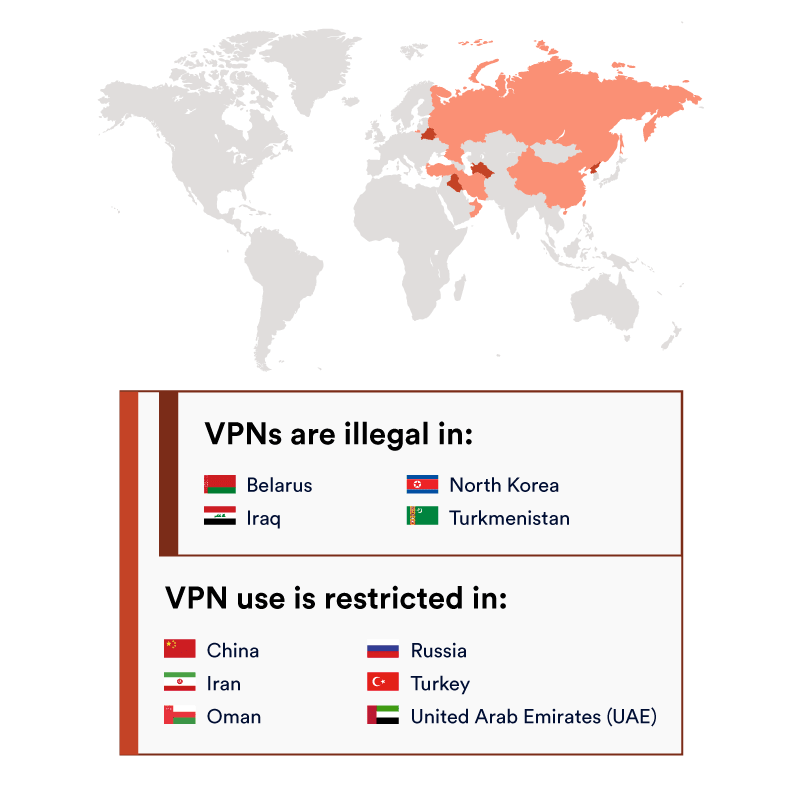
For some more historical info, there is this list on Wikipedia: https://en.m.wikipedia.org/wiki/Tor_(network)#Reception,_impact,_and_legislation
For a more US-centric FAQ, you can check: https://community.torproject.org/relay/community-resources/eff-tor-legal-faq/
Still, most countries don’t like random people to let other unidentified random people to do random stuff, most police officers are ill equipped or educated to deal with it, legislation hasn’t been tested in most places, and you’re running a hard to define, changing, and sometimes random level of risk.
we should have separate dark web(no CP) and dark web(CP)
Yes we should. How would you go about doing that?
Put it in the dark web’s terms of service.
Imagine trying to enforce such a thing on the dark web. What would you call the people who would end up with that job?
Start two dark webs, fill one with CP… and all the CP users will go to that one? Or something /s
Put a CP detector at dark web(no CP) exit nodes and throttle the speed to shit when triggered?
Oh yeah, packet sniffing exit nodes in a privacy oriented network will surely go down well and will have no unforeseen consequences
It’s been working fine for 20+ years already, with consequences foreseen from the beginning:
- Don’t trust exit nodes, they get the final packets and can do with them whatever they want.
- If you put identifying data in an unencrypted packet, the exit node will know who you are.
- If you send identifying data (encrypted or not) to a website, the website will know who you are.
- Trust destination websites only barely more than you’d trust them normally, and only as long as you keep the NoScript enabled.
- If your entry node colludes with your exit node, they might analyze data traffic patterns to try and identify you.
If you want to hide your porn habits from your techie flatmate with a logging router, Tor works great. If you’re a CIA agent in Iran wanting to send some report back home without getting found out, Tor works great. If you’re a whistleblower wanting to send an anonymous tip to the Washington Post, Tor also works great. If you’re curious to see that foreign mercenary group’s website that’s blocked in your country… SWIM had to try some different circuits, but Tor also worked there.
I mean it’s an exit node and the open web you don’t really get to complain about lack of privacy when leaving Tor.
OTOH, there’s a simple problem: That traffic is still likely encrypted. It’s not like Tor exit nodes do the TLS handshake, do they? That would indeed be much stranger than applying traffic shaping.
Sure, but preinstalling packet snooping on exit nodes as a feature still doesn’t sound like a great move, nevermind how stupid the idea is exactly because, like you said, HTTPS is a thing
How would that possibly work?