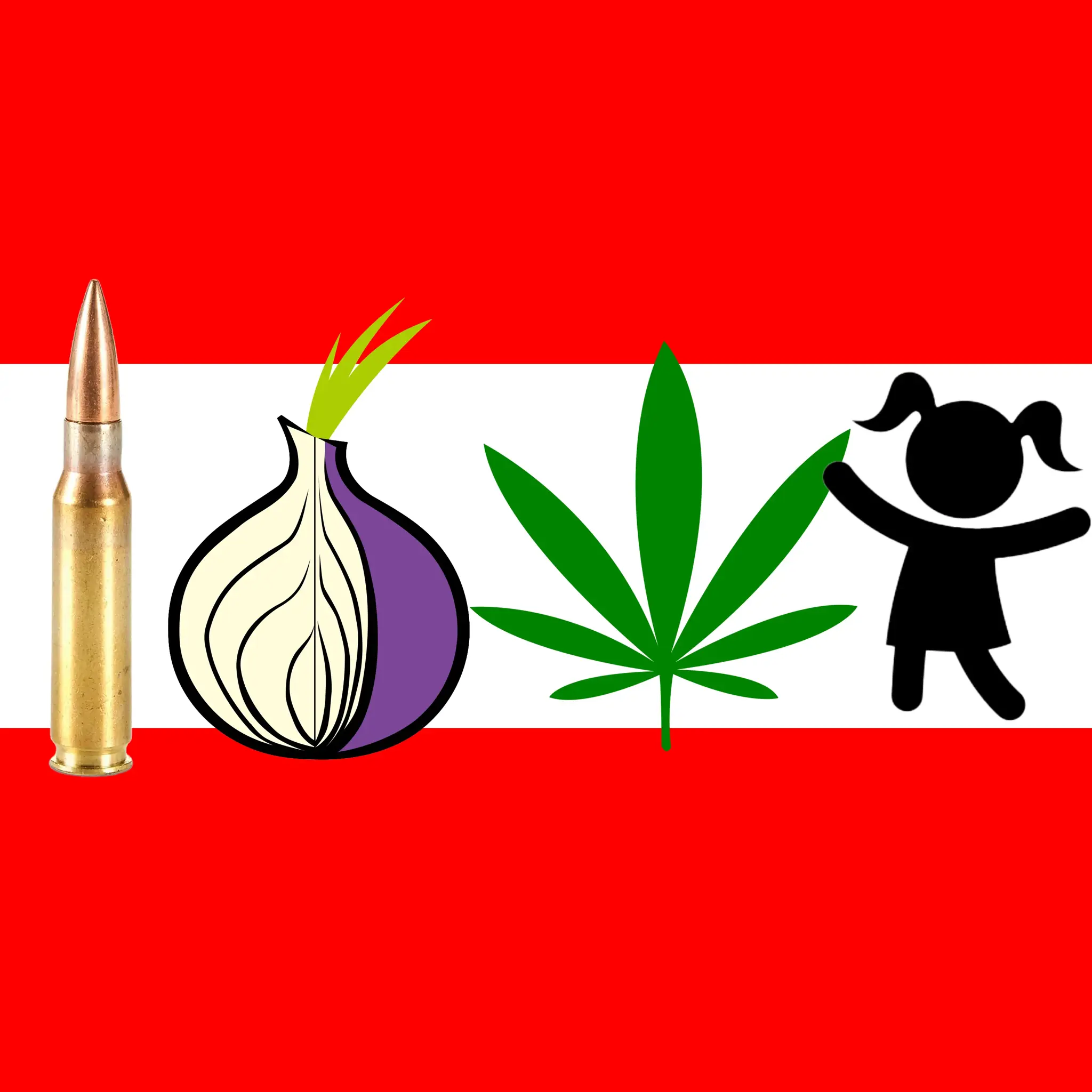
William Weber, a LowEndTalk member, was raided by Austrian police in 2012 for operating a Tor exit node that was allegedly used to distribute child pornography. While he was not arrested, many of his computers and devices were confiscated. He was later found guilty of supporting the distribution of child pornography through his Tor exit node, though he claims it was unintentional and he was simply supporting free speech and anonymity. He was given a 5 year probation sentence but left Austria shortly after. Though some articles portray him negatively, it is debatable whether he intentionally supported child pornography distribution or simply operated in the legal grey area of Tor exit nodes.


Put a CP detector at dark web(no CP) exit nodes and throttle the speed to shit when triggered?
Oh yeah, packet sniffing exit nodes in a privacy oriented network will surely go down well and will have no unforeseen consequences
It’s been working fine for 20+ years already, with consequences foreseen from the beginning:
If you want to hide your porn habits from your techie flatmate with a logging router, Tor works great. If you’re a CIA agent in Iran wanting to send some report back home without getting found out, Tor works great. If you’re a whistleblower wanting to send an anonymous tip to the Washington Post, Tor also works great. If you’re curious to see that foreign mercenary group’s website that’s blocked in your country… SWIM had to try some different circuits, but Tor also worked there.
I mean it’s an exit node and the open web you don’t really get to complain about lack of privacy when leaving Tor.
OTOH, there’s a simple problem: That traffic is still likely encrypted. It’s not like Tor exit nodes do the TLS handshake, do they? That would indeed be much stranger than applying traffic shaping.
Sure, but preinstalling packet snooping on exit nodes as a feature still doesn’t sound like a great move, nevermind how stupid the idea is exactly because, like you said, HTTPS is a thing